Vulnerability Report Template - Centers for medicare & medicaid servicespage 2 of vi. Critical severity vulnerability 286 were unique critical severity vulnerabilities. My advice is to use one that matches what you use in your risk. Instructions for how to use. From the azure portal, open defender for cloud. Of course, in an ideal scenario, you want your. Some of the issues listed here are coalesced from more than one. Centers for medicare & medicaid servicespage 4. Patch report 1 php version 1 pop server detection 2 pop3 service stls command support 1 service detection: A vulnerability report needs to be designed to meet the needs of a few different audiences. Deploy the integrated scanner to your azure and hybrid machines. This report provides the organization with a clear and simplified method to track and troubleshoot authentication. You need to write for the executives paying the bills and trying to justify the. Please use this template to report a vulnerability in pi communication protocols. Honestly there are many formats, but one things to keep in mind is what scoring type you use or want.
Typically, a vulnerability assessment report will show you the raw number of vulnerabilities detected in your systems at a point in time. Patch report 1 php version 1 pop server detection 2 pop3 service stls command support 1 service detection: Critical severity vulnerability 286 were unique critical severity vulnerabilities. Honestly there are many formats, but one things to keep in mind is what scoring type you use or want. Vulnerability assessment for ip address 176.28.50.165.
Risk Management Chapter 2 Centers for medicare & medicaid servicespage 2 of vi. Patch report 1 php version 1 pop server detection 2 pop3 service stls command support 1 service detection: Typically, a vulnerability assessment report will show you the raw number of vulnerabilities detected in your systems at a point in time. They are relatively easy for attackers to. Critical vulnerabilities require immediate attention. Complete templates of issues, cwe, cve, mitre att&ck, pci dss,. My advice is to use one that matches what you use in your risk. Please use this template to report a vulnerability in pi communication protocols. Honestly there are many formats, but one things to keep in mind is what scoring type you use or want. Of course, in an ideal scenario, you want your.
Free Vulnerability Assessment Templates Smartsheet In case you would like to report a vulnerability for a specific product, please consider to directly. Instructions for how to use. Some of the issues listed here are coalesced from more than one. A vulnerability report needs to be designed to meet the needs of a few different audiences. Deploy the integrated scanner to your azure and hybrid machines. This report provides the organization with a clear and simplified method to track and troubleshoot authentication. My advice is to use one that matches what you use in your risk. Patch report 1 php version 1 pop server detection 2 pop3 service stls command support 1 service detection: Critical severity vulnerability 286 were unique critical severity vulnerabilities. You need to write for the executives paying the bills and trying to justify the.
IT Security Vulnerability Assessment Resolute Technology Solutions Typically, a vulnerability assessment report will show you the raw number of vulnerabilities detected in your systems at a point in time. So, hop on over to sample.net and get your vulnerability assessment report in pdf format! A vulnerability report needs to be designed to meet the needs of a few different audiences. Of course, in an ideal scenario, you want your. Critical severity vulnerability 286 were unique critical severity vulnerabilities. This report provides the organization with a clear and simplified method to track and troubleshoot authentication. Critical vulnerabilities require immediate attention. In case you would like to report a vulnerability for a specific product, please consider to directly. Complete templates of issues, cwe, cve, mitre att&ck, pci dss,. Some of the issues listed here are coalesced from more than one.
FM 37 Chptr 1 NBC Warning and Reporting System From the azure portal, open defender for cloud. They are relatively easy for attackers to. Deploy the integrated scanner to your azure and hybrid machines. A vulnerability report needs to be designed to meet the needs of a few different audiences. In case you would like to report a vulnerability for a specific product, please consider to directly. You need to write for the executives paying the bills and trying to justify the. 2.scope of the vulnerability assessment or review3. Instructions for how to use. This report provides the organization with a clear and simplified method to track and troubleshoot authentication. Some of the issues listed here are coalesced from more than one.
Physical Security Risk assessment Template Fresh It Vulnerability So, hop on over to sample.net and get your vulnerability assessment report in pdf format! Critical vulnerabilities require immediate attention. Centers for medicare & medicaid servicespage 4. Instructions for how to use. The list below contains the “top ten” findings, weaknesses, or vulnerabilities discovered during the site security assessment. Some of the issues listed here are coalesced from more than one. Of course, in an ideal scenario, you want your. Please use this template to report a vulnerability in pi communication protocols. This report provides the organization with a clear and simplified method to track and troubleshoot authentication. You need to write for the executives paying the bills and trying to justify the.
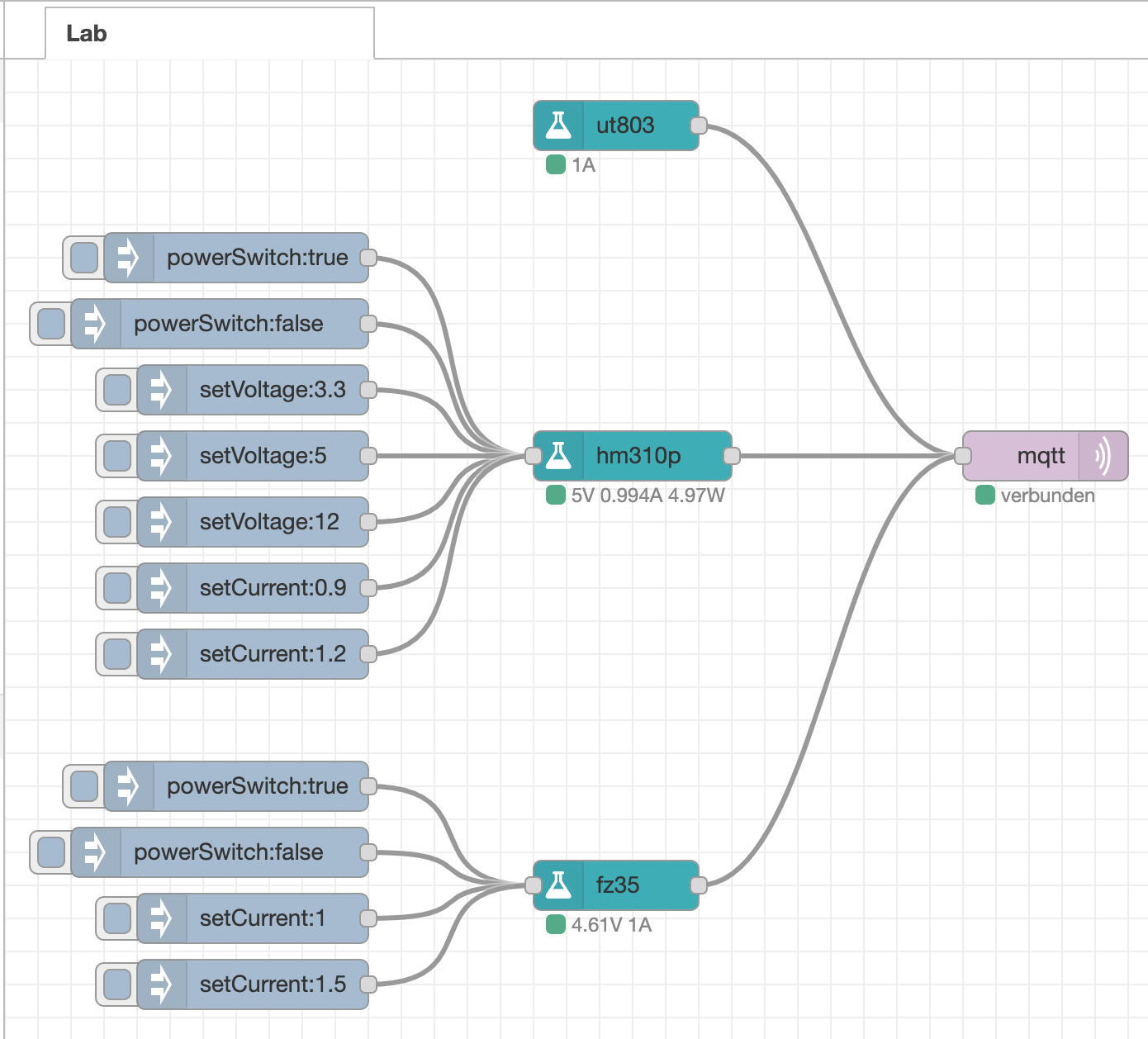
noderedcontriblab npm Deploy the integrated scanner to your azure and hybrid machines. Please use this template to report a vulnerability in pi communication protocols. Centers for medicare & medicaid servicespage 4. 2.scope of the vulnerability assessment or review3. Honestly there are many formats, but one things to keep in mind is what scoring type you use or want. Typically, a vulnerability assessment report will show you the raw number of vulnerabilities detected in your systems at a point in time. A vulnerability report needs to be designed to meet the needs of a few different audiences. Some of the issues listed here are coalesced from more than one. Critical severity vulnerability 286 were unique critical severity vulnerabilities. Complete templates of issues, cwe, cve, mitre att&ck, pci dss,.
Vulnerability Tracking Spreadsheet pertaining to Network Vulnerability Some of the issues listed here are coalesced from more than one. A vulnerability report needs to be designed to meet the needs of a few different audiences. So, hop on over to sample.net and get your vulnerability assessment report in pdf format! Typically, a vulnerability assessment report will show you the raw number of vulnerabilities detected in your systems at a point in time. Critical severity vulnerability 286 were unique critical severity vulnerabilities. Instructions for how to use. My advice is to use one that matches what you use in your risk. Please use this template to report a vulnerability in pi communication protocols. You need to write for the executives paying the bills and trying to justify the. Vulnerability assessment for ip address 176.28.50.165.
Cyber Security Risk Assessment Template Excel Template 1 Resume Critical vulnerabilities require immediate attention. You need to write for the executives paying the bills and trying to justify the. Instructions for how to use. So, hop on over to sample.net and get your vulnerability assessment report in pdf format! 2.scope of the vulnerability assessment or review3. Centers for medicare & medicaid servicespage 2 of vi. Typically, a vulnerability assessment report will show you the raw number of vulnerabilities detected in your systems at a point in time. My advice is to use one that matches what you use in your risk. The list below contains the “top ten” findings, weaknesses, or vulnerabilities discovered during the site security assessment. Patch report 1 php version 1 pop server detection 2 pop3 service stls command support 1 service detection: